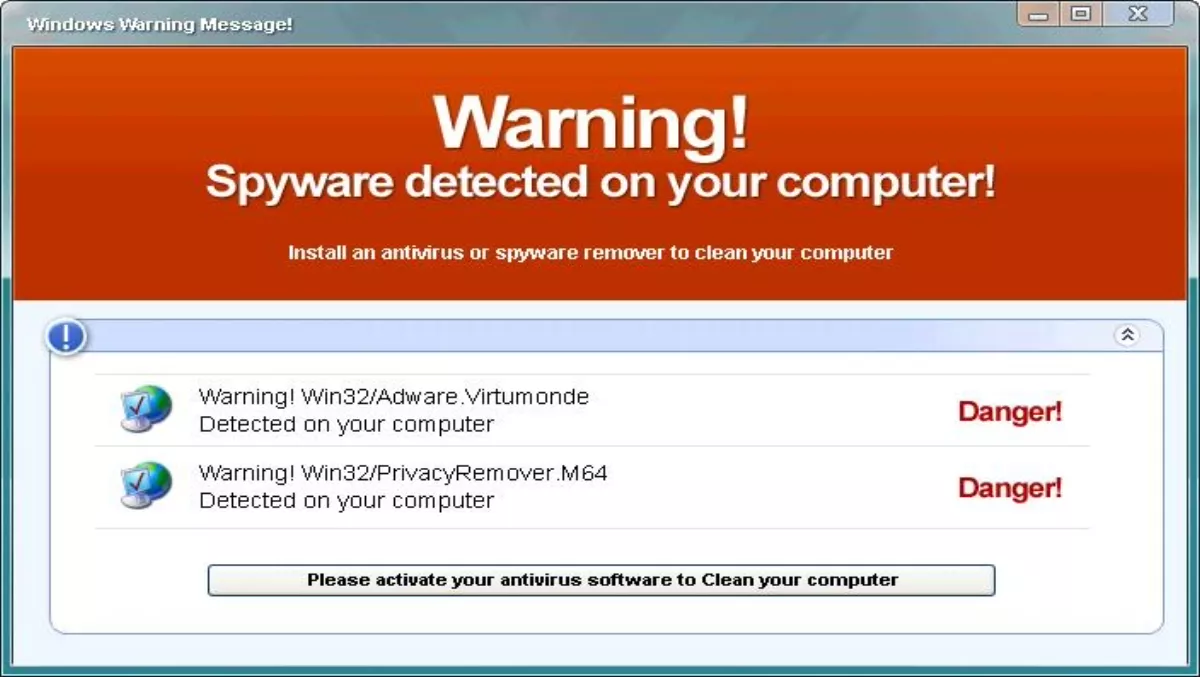
AVG's Community Powered Threat Report, Q4 2011, highlights the continuing success of fake antivirus products and Michael McKinnon, AVG (AU/NZ) security advisor says resellers could be missing out on sales because end-users believe they are already protected because they're running fake antivirus software. "It really highlights the importance of enquiring further as to what your customers are running and making sure what they are using is legitimate,” McKinnon says. The Community Powered Threat Report says in Q4 2011, AVG's LinkScanner blocked almost eight million attempts to redirect visitors to an installation of rogue antivirus software using the ‘second-click redirect mechanism'. The second-click infection method redirects to a fake antivirus scanner page that lures users into downloading and paying for an antivirus tool to ‘remove' the fictitious malware. "Another important aspect of this story is showing that the underworld of cyber crimes is organised,” AVG says. "Malicious websites do not only share traffic, they also share owners.” While the Community Powered Threat Report is a global report and no New Zealand breakdown is available, McKinnon says ‘there are definitely some cases in New Zealand'. "Resellers need to build awareness of the issue,” he says. "It's home and small business users who are affected and it really does affect so many people.” McKinnon says the report also highlights areas of opportunity for New Zealand resellers, particularly in areas such as mobile security, where he says resellers need to not only be able to advise clients on the products available, but offer practical tips, such as advice on remote wiping and PIN codes. "Resellers need to be mindful that they are the front line. Resellers have a responsibility, which I think a lot forget, to help ensure people are not being scammed or taken advantage of.” The report says stolen digital certificates in the mobile malware world are now a reality. "Malware targeting mobile devices is following the steps of its ancestor, PC malware,” AVG says. "Malware writers are using the same extremely sophisticated techniques when targeting mobile devices. In the last year we have seen an increase of using legitimate certificates, issued by certificate authorities to sign malware.” QR codes malware vehicle The report also flags the risks hidden in QR codes which ‘are being discovered as an ideal way to distribute malware to unsuspecting victims'. McKinnon says a perfect storm is brewing as the convenience of QR codes and the ability to download a mobile app combine with the already known security flaws of mobile phones. "Add to that that large brands are starting to use QR codes, providing almost a default trust factor...” he says. "It's so easy for users to scan the QR code and unwittingly download malicious applications that can very easily breach their privacy.” The report details how hackers can mislead users to scan QR codes that download malware into their mobile devices – a technique expected to gain momentum in 2012 and beyond as the user does not know what lies behind the QR code until the malware is already installed and running. Yuval Ben-Itzhak, AVG Technologies chief technology officer, says the convergence between computers and mobile phones applies to malware too. "As phones become more like computers, so do the risks. Many sophisticated tricks of the trade from computers are now being repurposed for phones. However, as phones are often tied into billing systems, the gains can be far greater.” McKinnon says there is plenty of scope for resellers to not only supply software but also provide managed services. "It's [an area] ripe to take opportunity of.”